Iran 'finds fix' for sophisticated Flame malware
- Published
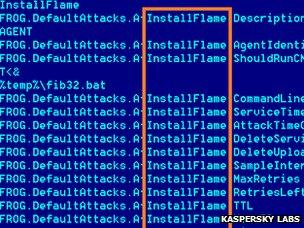
The sophistication of Flame helped it avoid detection by security software
Iran says it has developed tools that can defend against the sophisticated cyber attack tool known as Flame.
The country is believed to have been hit hard by the malicious programme which infiltrates networks in order to steal sensitive data.
Security companies said Flame, named after one of its attack modules, is one of the most complex threats ever seen.
Iran says its home-grown defence could both spot when Flame is present and clean up infected PCs.
Hard work
Iran's National Computer Emergency Response Team (Maher) said in a statement that the detection and clean-up tool was finished in early May and is now ready for distribution to organisations at risk of infection.
Flame was discovered after the UN's International Telecommunications Union asked for help from security firms to find out what was wiping data from machines across the Middle East.
An investigation uncovered the sophisticated malicious programme which, until then, had largely evaded detection.
An <link> <caption>in-depth look at Flame by the Laboratory of Cryptography and System Security</caption> <url href="http://www.crysys.hu/skywiper/skywiper.pdf" platform="highweb"/> </link> at Hungary's University of Technology and Economics in Budapest, said it stayed hidden because it was so different to the viruses, worms and trojans that most security programmes were designed to catch.
In addition, said the report, Flame tried to work out which security scanning software was installed on a target machine and then disguised itself as a type of computer file that an individual anti-virus programme would not usually suspect of harbouring malicious code.
Graham Cluley, senior technology consultant at security firm Sophos, said the programme had also escaped detection because it was so tightly targeted.
"Flame isn't like a Conficker or a Code Red. It's not a widespread threat," he told the 91╚╚▒Č. "The security firm that talked a lot about Flame only found a couple of hundred computers that appeared to have been impacted."
Mr Cluley said detecting the software was not difficult once it had been spotted.
"It's much much easier writing protection for a piece of malware than analysing what it actually does," he said. "What's going to take a while is dissecting Flame to find out all of its quirks and functionality."
It is not yet clear who created Flame but experts say its complexity suggests that it was the work of a nation state rather than hacktivists or cyber criminals.
Iran suffered by far the biggest number of Flame infections, suggest figures from <link> <caption>Kaspersky Labs in a report about the malicious programme</caption> <url href="http://www.securelist.com/en/blog?weblogid=208193522" platform="highweb"/> </link> .
Kaspersky said 189 infections were reported in Iran, compared to 98 in Israel/Palestine and 32 in Sudan. Syria, Lebanon, Saudia Arabia and Egypt were also hit.
In April, Iran briefly disconnected servers from the net at its Kharg island oil terminal as it cleared up after a virus outbreak - now thought to be caused by Flame.
In the same statement that announced its home-grown detection tool, Iran said Flame's "propagation methods, complexity level, precise targeting and superb functionality" were reminiscent of the Stuxnet and Duqu cyber threats to which it had also fallen victim.
Stuxnet is widely believed to have been written to target industrial equipment used in Iran's nuclear enrichment programme.
- Published28 May 2012
- Published23 April 2012
- Published8 March 2012
- Published26 April 2012